The Windows Operating System or Windows OS statistically has a worldwide share of 33.1%, just after the android market. The Microsoft Windows system had initially developed this OS in the 1980s.
It has come a long way since then with several updates released for its version making the OS better and better. The latest version is Windows 10 with the latest patch being released on 25th March 2020.
The initial update had been full of bugs and errors. With later fixed versions, the errors and bugs were resolved. But one such error persisted.
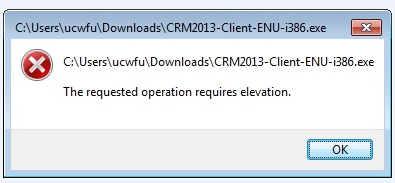
It requested the users to grant administrator access to open file locations that require administrative permission. Although the user is the administrator in most scenarios, this error keeps on showing up even when the user tries to modify external data.
Initially, several BETA fixes were suggested. Some of them worked out temporarily and many didn’t even cut it to the list of viable solutions.
Read Also:
- 0xc000007B
- Ethernet Doesn’t Have a Valid IP Configuration
- Windows Can’t Communicate With The Device or Resource
Contents
How to Fix The Requested Operation Requires Elevation in Windows 10
These solutions are very much based on trials and success. Also, they were gathered based on the efficiency of these fixes. After thousands of debugging sessions, the following fixes are fully efficient in solving the given error. Please follow step by step for guaranteed results.
Solution 1: Disabling The UAC
Before jumping into the whole process, one of the concepts has been discussed in brief that’ll be useful to understand this fix more effectively. User Access/Account Control or UAC is an elementary control enforcement feature in Microsoft Windows that was introduced into the later versions of the OS released in 2008 mainly.
UAC is mainly prompted when there are changes made to the system settings or when files and applications are run as an Administrator. There are several other reasons for this prompt but these two are the main ones.
Coming back to the fix, it is important to mention that administrative privileges are provided to the owners and trusted users only due to its ability to modify sensitive files and application components.
Recent updates are causing the UAC to pop up more often than required. This has made application run checks more common and frustrating. This can be fixed by disabling the UAC. Follow the steps given below to execute this fix effectively:
Step 1: Click on the Search Tab provided on the taskbar to search for the required settings.
Step 2: Search for the keyword “UAC”.
Step 3: Click on “Change User Account Control Settings”.
Step 4: Drag the Slider down to “Never notify” and click ok. This will do the trick.
Alternatively,
Step 1: Press the “Windows+ R” combination to bring up the Run Prompt.
Step 2: Type “cmd” to bring up the command console.
Step 3: Enter the following line to disable the UAC and press Enter.
C:\Windows\System32\cmd.exe /k %windir%\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f
Solution 2: Adding Domain Admins Group To The Local Administration Group
Domain Admin/Administrator is a user that can configure and edit information in Active Directory running on Windows OS. The Domain Admin Account has complete control over the user rights and permissions and can change them to adjust and configure the user interface.
A group of Domain Admin has complete control over the current domains that are under their servers. In contrast to Domain Admins, Local Admins have partial control over the domain, i.e., only their own local server.
They do not have the power to configure directory files in other servers. The following method is useful when one or more users are unable to register their computers to other servers in the same domain.
Using Group Policy:
Step 1: Press “Windows + X” to bring up the features menu on Windows 10.
Step 2: Click on “Windows Powershell (Admin)” to run the Windows PowerShell command console on Admin mode.
Step 3: Type “gpedit” to open the group policy editor. After this, create a New Group Policy Object. Name it according to choice. For example “LocAdmins”.
Step 4: Go to Computer Configurations> Policies>Windows Settings>Security Settings>Restricted Groups. Add a new group by right clicking on the “Restricted Groups” tab and selecting “Add Group”.
Step 5: Add members of the new group and then select the group of which it will be added to. (This group to which it will be added will appoint all the names of the members as current Admins of the Local Group. Once granted Admin rights, they will have full modification power over local data).
Step 6: After clicking on Add of the “This group is a member of” a dialogue box will pop up where local admin group names can be searched for.
Step 7: Check names to make sure the group exists and click OK.
This method should allow the new group of users to be added to the local administrator’s group granting access to directory files and their modification.
After completing these steps, apply the Group Policy to any preferred unit of organization. Right, Click and select “Link an Existing GPO”. Select the required group and close the window. Restart the computer
To Check and Run the Group Policy:
The Local network computers are interconnected and hence the new admin group should have control over them instantaneously.
Step 1: Log on to a computer on the same local network.
Step 2: Bring up the Windows Power shell prompt by pressing Windows+X and type”gpupdate/force”
This will bring up the local admins group.
Solution 3: Disabling The Admin Approval Mode For Built-in Administrator
The Admin Approval mode frequently overrides to ask for permission while executing the opening and modifying admin/directory files even through the user himself is the Administrator.
This prompt acts as an elevator which enforces administrative privileges even through the server is accessed by the admin account itself. This policy is located in the Group Policy Editor itself and can be disabled via many ways. The easiest methods are discussed below:
Step 1: Click Windows+R to bring up the command console. Or similarly Press Windows+X to bring up Windows Powershell(Admin) Option to launch the Powershell console. Both ways are correct.
Step 2: Type in “gpedit.msc” to open the Local Group Policy Editor. Follow the next steps to continue:
Step 3: Computer Configuration>Windows Setting>Security Settings>Local Policies>Security Options.
Step 4: Then Scroll down to the bottom of the shown list and click on “User Account Control: Admin Approval Mode for the Built-in Administrator account”.
Step 5: Open it and select on Disable option.
Step 6: Press OK.
Restart the computer to set the system to acknowledge the change made. This should remove the prompt of elevation that requires permission to edit even by the admin account.
Solution 4: Changing Ownership Of Files
The ownership of files in a computer depends on the permissions of the files usually set by the user himself or the administrator. The ownership decides if the file can be modified by other users or not. The terminology of ownership in Linux OS spreads over three terms.
But this fix will only be for Windows OS users who has Windows 7 or above. This solution is for users who face problems during file access in local drive of their own PC or LAN (Local Area Network) computers.
This involves changing the ownership of the said problematic files to give full user rights to access, modify and delete any file. This may require administrator permission to change ownership.
Step 1: Right click on the file of which the ownership is to be changed.
Step 2: Click on “Properties” and select the “Security” tab.
Step 3: Click on the “Advanced” option presented below. This should open the pop-up dialogue box screen that allows modification of ownership.
Step 4: Under the owner tab, there is an option for “change” that runs only as an admin elevation. Click on it.
Step 5: It will then display another pop-up where names should be entered to change the ownership to that name account. In case of more precision, click on the “Advanced” option below to search for valid usernames that are already present in the system logs.
Step 6: After this, the same steps should be followed with all the subfolders within the folder to completely change the ownership of all the files.
Alternatively, a quicker solution is to use the cmd console to take control and ownership of the required files.
Step 1: Press the Windows+R and type in “cmd”.
Step 2: Enter the following line to change ownership as required:
TAKEOWN /F <xxxxx>
*<xxxxx> should be replaced with the actual file name>*
Step 3: After the successful execution of the command, the following line should appear,
“SUCCESS: The file (or folder): “filename” now owned by user “Computer Name\User name”
Step 4: This method will quickly grant ownership of the required files to the user from which the command has been executed. For Advanced ownership rights, follow the former method prior to the quicker one.
Solution 5: Running The Program As Administrator
Running as an Administrator means that the system is allowed to execute programs and software based on privileges owned by an Admin. This means that the programs and software are harmless and can be used on the system without raising red flags.
Run as an Admin grants the user unrestricted access to the files and system data that are present in the computer. The following methods are used to run a program as an Admin:
Step 1: Right click on the file or program that is to be run.
Step 2: Click on the “Run as Administrator” option.
The next method will always allow the file or program to run as administrator.
Step 1: Right-click on the program and select “Properties”.
Step 2: Under the shortcut tab, click on the “Advanced” option and check on the “Run as administrator” box.
Read Also:
Conclusion
All the above methods have been tested and run for guaranteed efficiency. The problem of elevation is a troublesome one and hence it should be taken care of. As Moliere said, “The greater the obstacle, the more glory in overcoming it”.
This elevation is the obstacle every diligent person should take care of to avoid wastage of time and peace in allowing/granting unnecessary permissions.

![WLDCore.dll is Missing Error in Windows 10 [RESOLVED] WLDCore.dll is Missing Error](https://howandwow.info/wp-content/uploads/2019/09/WLDCore.dll-is-Missing-Error.jpg)




![Err_Connection_Reset Error in Chrome [RESOLVED] Fix Err_Connection_Reset Error in Google Chrome](https://howandwow.info/wp-content/uploads/2019/09/Fix-Err_Connection_Reset-Error-in-Google-Chrome.jpg)
![DNS_Probe_Finished_No_Internet Error [RESOLVED] Fix DNS_Probe_Finished_No_Internet Error](https://howandwow.info/wp-content/uploads/2019/09/Fix-DNS_Probe_Finished_No_Internet-Error.jpg)
![Err_Cache_Miss in Google Chrome Error [RESOLVED] Err_Cache_Miss in Google Chrome Error](https://howandwow.info/wp-content/uploads/2019/08/How-to-Fix-Confirm-Form-Resubmission-Error.jpg)



![Steam Missing File Privileges Error [RESOLVED] How to Fix Steam Missing File Privileges](https://howandwow.info/wp-content/uploads/2020/07/How-to-Fix-Steam-Missing-File-Privileges-Error-100x70.jpg)



![SIM Not Provisioned MM#2 Error [RESOLVED] SIM Not Provisioned MM#2](https://howandwow.info/wp-content/uploads/2020/03/SIM-Not-Provisioned-MM2.jpg)